GhostClaw, a macOS infostealer, is spreading through GitHub repositories and developer tools, and it works because routine install habits make running malware feel completely normal.
GhostClaw is spreading across GitHub
GhostClaw is spreading across GitHub
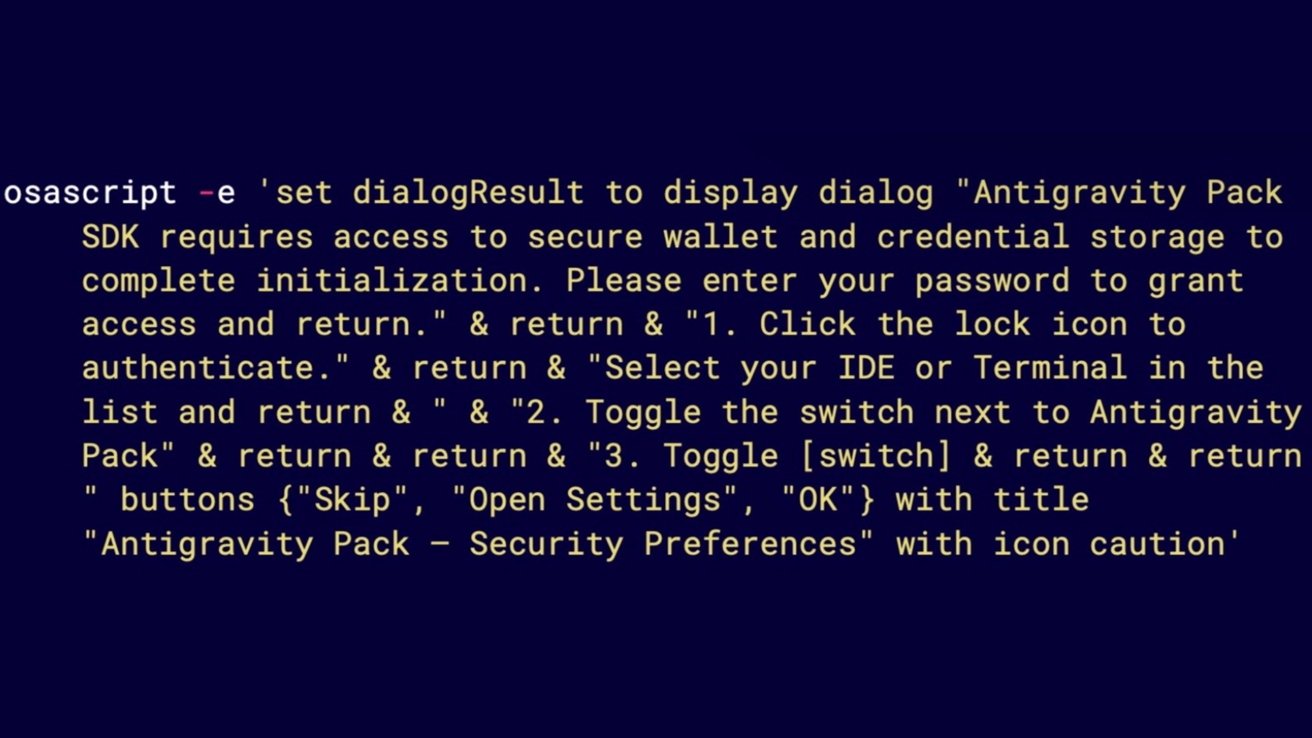
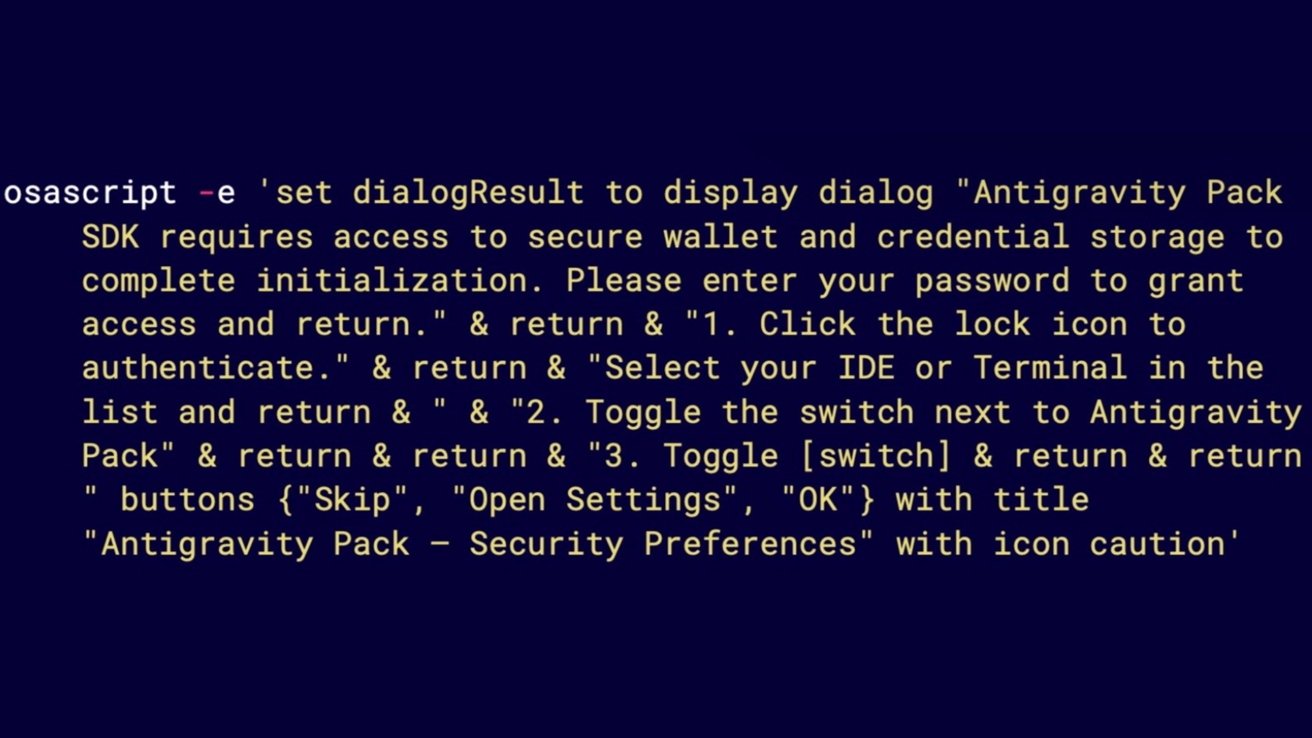
Jamf researchers tracked the campaign’s shift from npm packages to GitHub repositories and AI-assisted development environments. The payload, a macOS infostealer, blends into expected behavior rather than exploiting software.
Developers regularly pull code from GitHub, follow README instructions, and run install commands without much hesitation. Familiar patterns build trust, and GhostClaw slips directly into that routine.